 AppMakr is a webapp that lets you design iOS apps with a WYSIWYG editor. It's free to use, and you can create your very own app in just a few minutes.
AppMakr is a webapp that lets you design iOS apps with a WYSIWYG editor. It's free to use, and you can create your very own app in just a few minutes.AppMaker for iPhone
 AppMakr is a webapp that lets you design iOS apps with a WYSIWYG editor. It's free to use, and you can create your very own app in just a few minutes.
AppMakr is a webapp that lets you design iOS apps with a WYSIWYG editor. It's free to use, and you can create your very own app in just a few minutes.SoundCloud - We Move Music
Once you sign up you'll be encouraged to upload your own tracks and send them around. This is very quick and easy to do if you've got your own music (that you wrote) to share. If not, you can start browsing
Try it..
ManyEyes--Visualization Application from IBM
Know more..
Windows Live Essentials 2011
Download here...
Facebook and Skype Plan Integration
Read more..
Rainmaker~Supercharge your Google Contacts
Rainmaker helps you keep your contact information up-to-date by letting your contacts do it for you. Link your Twitter, Facebook, and LinkedIn accounts to Rainmaker and it'll update your Google Contacts with any new information. You can perform this action manually for individually contacts or allow Rainmaker to handle it for you automatically
http://rainmaker.cc/
Live FIFA ~ Don't miss it
But there's more, you can also watch Live TV channels on your pc, by using the Live TV section.
Feel free to browse around: After a while you will see Myp2p is the best guide for all your Live TV and Live sports.
http://www.myp2p.eu/
Salix O/S
- one application per task on the installation ISO
- fully backwards compatible with Slackware
- optimized for desktop usage
- high quality package repositories with dependency support
- incredibly fast package tools
- simple & fully localized system administration tools
- nice artwork
- installation ISO fits on a single CD
- supports 32-bit and 64-bit architectures
Read more N Download here
Inkscape~Draw Freely
Inkscape supports many advanced SVG features (markers, clones, alpha blending, etc.) and great care is taken in designing a streamlined interface. It is very easy to edit nodes, perform complex path operations, trace bitmaps and much more. We also aim to maintain a thriving user and developer community by using open, community-oriented development.Software can be downloaded from developer's website
Download
Juice~The Podcats Receiver
Juice lets users select and download shows and music and play whenever they want on their iPods, portable digital media players, or computers automatically
Juice uses RSS (really simple syndication) to "feed" files to
your computer. RSS usually involves headlines and text, but we've devised a way to have it move audio files. Once you've installed Juice, you can select podcasts to subscribe to in two different ways: Either clicking the selection button to see a directory of available podcasts or enter a URL for a podcast you've found on your own. You can set the scheduling options so that Juice scans for new downloads as often as you like, or you can control it manually. When it is done downloading new files, it adds them to your library, all ready to be played or synched to your MP3 device. Software can be downloaded from developer's website
Download
Play & Win Mobile Phone
Read more & Play
Breach of Trust
Similarity~find duplicate music files
Software can be downloaded from developer's website
Avatar (Two-Disc Blu-ray/DVD Combo) [Blu-ray]
R U getting emails from your own Email ID
Report the email as spam
Reporting spoofed emails as spam helps to ensure that future emails from the spammer source behind the email will go into your spam folder. Please be assured that by reporting the email as spam, you are not blocking or reporting yourself. You are just helping us identify the source of the spoofed email.
Delete your email address from your Address Book
By having your own email address in your Address Book it reduces the scrutiny applied to mail that appears to being sent from you to you.
Change your password If you suspect your account has been compromised, check your Sent folder for any emails that weren't sent by you. If you see any such emails, please change your password immediately.
Thanx
IObit~Uninstaller
Download...
Vista won't remember mapped network drive password ?
So finlally i got the solution...
Here I'm sharing with you..
1.You have to create one .vbs file with following script.
2. open notepad
3. type or copy following script..
4.Set objNetwork = CreateObject("WScript.Network")objNetwork.MapNetworkDrive "N:", "\\PCName\SharedFolder", , "username", "password"
Be sure about the mapped drive letter and folder path...
You can add more mapped drives by copying that last line as many times as you need.
4.Now save the file inside the "startup" folder..with any name but put extension .vbs(startup folder can be in this position location C:\Users\uk\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup
Thats it...
Now reboot the pc..next time it will not ask the login detail...
PenyuLocker~A free folder locker
PenyuLocker is a small tool to secure your folder. With PenyuLocker, you can lock or unlock any folder with a given password. This will prevent unauthorised person from having access to any sensitive or confidential information in your computer.
Once locked, it will display the folder icon as a recycle-bin icon from your windows explorer. If you empty your recycle-bin, it wouldn't effect any files in your locked folder.
To unlock the folder, run PenyuLocker software. Browse to the previously locked folder and select "Unlock" function. It will again ask you for a password. Make sure you remember the password.
Free Download..
WeTransfer
File transfer services tend to be distinctly not user friendly. From ugly and hard to navigate interfaces to forced wait times to annoying captcha and more wait times, it's not a whole lot of fun to be the sender or receiver. WeTransfer strives to eliminate the hassle of transferring files that are too big to fit in an email. You can select as many files as you want to send at one time—as long as you stay below the 2GB per transfer cap—and send an email notice to 1-20 recipients with a note attached.
Go for it..
iReboot~multiple rebooter
 iReboot is NeoSmart Technologies' simple yet effective reboot helper tool. iReboot sits in your taskbar at startup (only taking up 400KB of memory!) and lets you choose which operating system you want to reboot into. Instead of pressing restart, waiting for Windows to shut down, waiting for your BIOS to post, then selecting the operating system you want to boot into (within the bootloader time-limit!); you just select that entry from iReboot and let it do the rest! If you liked EasyBCD, you'll just love iReboot!
iReboot is NeoSmart Technologies' simple yet effective reboot helper tool. iReboot sits in your taskbar at startup (only taking up 400KB of memory!) and lets you choose which operating system you want to reboot into. Instead of pressing restart, waiting for Windows to shut down, waiting for your BIOS to post, then selecting the operating system you want to boot into (within the bootloader time-limit!); you just select that entry from iReboot and let it do the rest! If you liked EasyBCD, you'll just love iReboot!BulkFileChanger
Read More and Download
Driver Backup
Double Driver is a very simple and useful tool which not only allows you to view all the drivers installed on your system but also allows you to backup, restore, save and print all chosen drivers.
It can be quite difficulty for example to find drivers for hardware installed in a notebook if the operating system has to be setup again. Luckily Double Driver can now lend you a hand with that and save you a lot of time.Double Driver is freeware.
Double Driver Features.
List, save, and print drivers details
Backup drivers from current Windows
Backup drivers from non-live/non-booting Windows
Backup drivers to structured folders, compressed (zipped) folder, and self-extracting capability
Restore drivers from previous backup
Available in GUI and CLI application
Portable (no installation required)
3D Album
 Photo! 3D Album gives you an exciting opportunity to create stunning 3D albums where you will see your photos in the dreamlike environment of picturesque 3D galleries. 3D albums can be viewed in automatic mode, when the program itself guides you through the gallery halls.
Photo! 3D Album gives you an exciting opportunity to create stunning 3D albums where you will see your photos in the dreamlike environment of picturesque 3D galleries. 3D albums can be viewed in automatic mode, when the program itself guides you through the gallery halls.When A Hard Drive Fails
 When a hard drive crashes, you can lose all your data. Corrupt hard drives happen out of the blue and for seemingly no good reason. If your hard drive fails, what can you do?One option is to call a hard drive recovery company. If your data is worth a lot of money to you, you can pay a forensic computer company to get the data off your hard drive. Before you write a check though, try a little Do-It-Yourself first.
When a hard drive crashes, you can lose all your data. Corrupt hard drives happen out of the blue and for seemingly no good reason. If your hard drive fails, what can you do?One option is to call a hard drive recovery company. If your data is worth a lot of money to you, you can pay a forensic computer company to get the data off your hard drive. Before you write a check though, try a little Do-It-Yourself first.Place the hard drive inside of a zip top freezer bag. (don't buy a cheap bag.)
Place the wrapped hard drive inside of ANOTHER zip top freezer bag. (yes, you need to do this) (see figure 1 below)
Place the double wrapped hard drive in the coldest part of your freezer.
Leave the hard drive in the freezer for 12 hours at least. You want it good and cold! (see figure 2 below)
Once very chilled, install the hard drive in your computer and start pulling off data. Begin with the most valuable data.
At some point, the hard drive will fail again. When it does, mark the last successfully copied data, pull out the hard drive, double wrap it again and stick it in the Chill Chest for another 12 hours.
You may need to do this a number of times to get all the data you want, or until the hard drive stops working completely.
Total PC Defender 2010 ~ A Malware
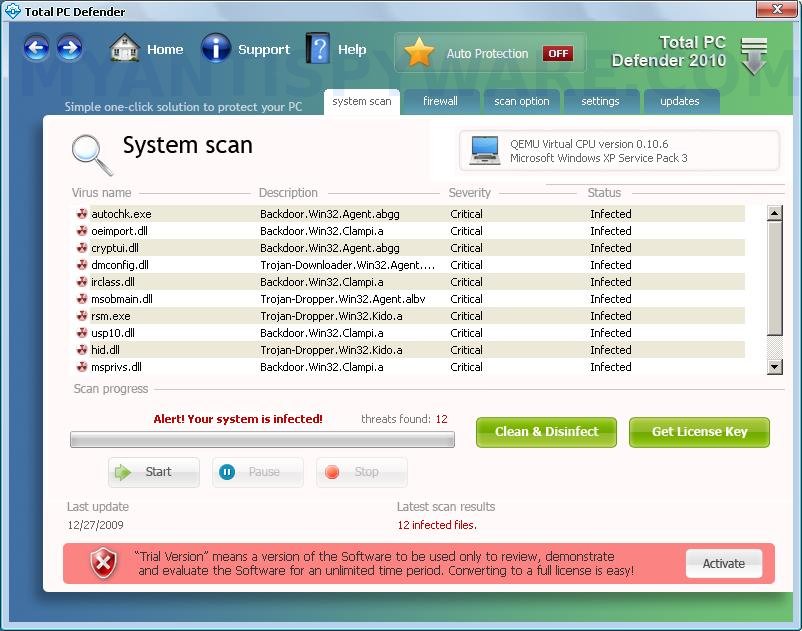 Total PC Defender is a malware that pretends to be an Antivirus when in reality it is a malware. It is a wolf in sheep's clothing. It conducts a fake scan of your system; you are warned by a fake alarm that there are more malwares on your system. It’s true indeed, there is really a malware in your system but I think the only malware on your system is Total PC Defender (AKA TotalPCDefender). It invites you to purchase a license to remove malware, do not, it's a scam, you need a license for a malware?
Total PC Defender is a malware that pretends to be an Antivirus when in reality it is a malware. It is a wolf in sheep's clothing. It conducts a fake scan of your system; you are warned by a fake alarm that there are more malwares on your system. It’s true indeed, there is really a malware in your system but I think the only malware on your system is Total PC Defender (AKA TotalPCDefender). It invites you to purchase a license to remove malware, do not, it's a scam, you need a license for a malware? Download this free removal tool for Total PC Defender
Extract it
Launch
Click on the delete button
Total PC Defender will be removed from your system in 10s. Restart your computer when it’s finished
WinPenPack
 winPenPack is an applications environment of Free Softwares, modified for being run and used from an USB pendrive, without need of installation. The removable device, so, is no more a simple data container, but becomes a really self-contained environment, within programs and documents are homogeneously integrated."Portable" softwares included into winPenPack does not need to be installed, does not write their settings into host PC, and can be easily carried between multiple computers through any external device, as removable hard disks or USB pendrives.After inserting the USB pendrive into a free USB port of host PC, user will have immediately available a collection of pre-configured and ready to use programs, subdivided in categories and executable through a practical menu, analogue to Windows menu Start, the winPenPack Launcher. User will feel as is working on its own PC, with web browsers, e-mail clients, image and drawing editors, chat clients, PC maintenance and security, school, development. All he needs, always available. All these features make winPenPack extremely useful in any field.
winPenPack is an applications environment of Free Softwares, modified for being run and used from an USB pendrive, without need of installation. The removable device, so, is no more a simple data container, but becomes a really self-contained environment, within programs and documents are homogeneously integrated."Portable" softwares included into winPenPack does not need to be installed, does not write their settings into host PC, and can be easily carried between multiple computers through any external device, as removable hard disks or USB pendrives.After inserting the USB pendrive into a free USB port of host PC, user will have immediately available a collection of pre-configured and ready to use programs, subdivided in categories and executable through a practical menu, analogue to Windows menu Start, the winPenPack Launcher. User will feel as is working on its own PC, with web browsers, e-mail clients, image and drawing editors, chat clients, PC maintenance and security, school, development. All he needs, always available. All these features make winPenPack extremely useful in any field.Download here..
MapQuest~iphone N ipod
 MapQuest® 4 Mobile brings over a decade of digital mapping experience to your iPhone® with unique features to help you get where you’re going. Try Voice-Guidance, our latest addition to Driving Directions, for a more hands-free experience!Few people know that MapQuest actually produced paper maps prior to becoming an Internet icon. In the future, people may be surprised to find that there was ever a time when mapping wasn't available on the mobile phone. Whatever the medium, we want to help get you there. MapQuest® 4 Mobile brings our unique 'secret sauce' to your iPhone®. Download it today.
MapQuest® 4 Mobile brings over a decade of digital mapping experience to your iPhone® with unique features to help you get where you’re going. Try Voice-Guidance, our latest addition to Driving Directions, for a more hands-free experience!Few people know that MapQuest actually produced paper maps prior to becoming an Internet icon. In the future, people may be surprised to find that there was ever a time when mapping wasn't available on the mobile phone. Whatever the medium, we want to help get you there. MapQuest® 4 Mobile brings our unique 'secret sauce' to your iPhone®. Download it today.- NEW! Voice
- NEW! Off-Route Assistance
- Energy savings mode
- Walking directions (pedestrian mode)
- Save Maps and Routes
- Make your own my position icon
Http File Server~Share your files

It's different from classic file sharing because it uses web technology to be more compatible with today's Internet.
It also differs from classic web servers becauseit's very easy to use and runs "right out-of-the box". Access your remote files, over the network.
It has been successfully tested with Linux Wine System.
~Virtual file system .
~Highly customizable.
~HTML template .
~Bandwidth control.
~Easy/Expert mode.
~Log .
~Full control over connections .
~Accounts .
~Dynamic DNS updater .
~Its free. Download here ....
Woobius--Makes Design & File Sharing Easy
 Woobius is a new file sharing and project collaboration online solution serving architects, engineers and other design professionals who need to share drawings and other documents with their team. As a web-based Software-as-a-Service (SaaS) platform, it is accessible from virtually any internet-connected computer. The idea is to keep file sharing simple and user friendly, stripping it of unnecessary bells and whistles to capitalize on the power of collaboration.All you need is your web browser¹ and you're good to go.Upload photos, take screenshots, and draw live with as many people as you like. Woobius Eye will soon be available on a number of smart phones and devices In fact, if you see a little pulsating cursor in this middle of this page then you're already connected
Woobius is a new file sharing and project collaboration online solution serving architects, engineers and other design professionals who need to share drawings and other documents with their team. As a web-based Software-as-a-Service (SaaS) platform, it is accessible from virtually any internet-connected computer. The idea is to keep file sharing simple and user friendly, stripping it of unnecessary bells and whistles to capitalize on the power of collaboration.All you need is your web browser¹ and you're good to go.Upload photos, take screenshots, and draw live with as many people as you like. Woobius Eye will soon be available on a number of smart phones and devices In fact, if you see a little pulsating cursor in this middle of this page then you're already connectedNoVirusThanks/Hijack Hunter/Threat Killer/Malware Remover/Websites Cop(all free)
 NoVirusThanks Malware Remover is an application designed to detect and remove specific malware, trojans, worms and other malicious threats that can damage your computer. It includes also the ability to remove rogue software, spyware and adware.
NoVirusThanks Malware Remover is an application designed to detect and remove specific malware, trojans, worms and other malicious threats that can damage your computer. It includes also the ability to remove rogue software, spyware and adware.Scanning time is very fast and does not use or need much memory even with other high-resource programs are running.
o Remove Rogue Software and Unwanted Applications
o Remove Trojans, Spyware and Worms
o Quick Scan and Full Scan
o Scan Processes
o Scan Modules
o Backup of Files and Folders
o Fast Scanning
o Easy to use
o Manual Update of Database
o Multilingual
USB Guardian - Scan USB for Worms and Viruses
USB Guardian allows you to safely enjoy file sharing using just an USB thumbdrive for copying the files . Movies, mp3s, documents and pictures can be copied from one computer to another without worrying of getting infected with worms and viruses trough USB drive.
USB thumbdrives have become a comodity and this fact is actively being exploited by criminals who have developed special viruses and worms which infect USB storage devices like thumbdrives, cameras and even mobile phones. The interface is very clean and well organized so that one can access all functions with minimum effort.
Download....
AVG Rescue CD--A powerful toolset for rescue & repair of infected PC
Download..







